If you're a marketer, MD, CEO or CFO looking to protect your organisation from fraud and phishing attacks while controlling the way your domain is used across trusted external channels, then you need to understand what DMARC is – and how it works.
DMARC (Domain-based Message Authentication, Reporting & Conformance) is an email authentication protocol that provides improved security capabilities over legacy protocols like SPF (Sender Policy Framework) and DKIM (DomainKeys Identified Mail).
In this blog post we'll be exploring what DMARC does exactly, how it can benefit organisations of all sizes by providing more secure emails for customers and staff alike - as well as outlining the different kinds of reports organisations have access to that allow them to track progress in real time when implementing their own policies.
Let's start with understanding email authentication.
What is Email Authentication?
Email authentication is a technical solution that assists internet service providers to more accurately identify the sender of an email which in turn helps reduce the amount of spam, phishing, and spoofing emails.
Email authentication relies on three standards that cover different areas of email authentication to create a comprehensive and layered approach.
1. Domain-based message authentication, reporting and conformance (DMARC)
2. Domain Key Identified Mail (DKIM)
3. Sender Policy Framework (SPF)
DMARC (Domain-based message authentication, reporting and conformance)
DMARC (Domain-based Message Authentication, Reporting & Conformance) is an email authentication protocol that builds on top of DKIM and SPF (Sender Policy Framework).
It helps to protect against phishing attacks by providing a way for senders and receivers to agree on what kind of authentication should be used when sending emails.
DMARC also provides feedback to senders about how their messages are being handled by receivers.
DMARC is a technical standard that needs to be set up by the sender to help authenticate and validate their identity to the receiver.
Simply put, DMARC helps an email receiver system identify whether an email is or is not sent from an organisation’s approved domains, and then tells the receiver systems how to appropriately deal with the unauthorised email.
DKIM and SPF have limited abilities when verifying emails.
For example, SPF does not work when messages are forwarded on and, as SPF only checks the header from address (the address that is visible to the end-user) it cannot protect against spoofing emails.
To overcome these limitations, businesses should employ DMARC alongside DKIM and SPF as a layered approach that will create a more secure and reliable process to help eliminate spam, phishing, and spoofing emails.
DKIM and SPF provide a framework to ensure the integrity of an email, however, DMARC allows for more control for the sender to help them ensure their email is received correctly and is the only way for senders to identify to the receiver that the email they are sending is in fact from them.
The elements DMARC adds are Identity Alignment, Policy Management and Reporting.
1. Identity Alignment
Identity Alignment allows senders more control of how their emails are authenticated, which helps to ensure that the end-user receives the original sent email.
2. Policy Management
Policy Management lets senders check the ‘from’ address that is shown in the email to the end-user. Policy Management also provides instructions on what to do upon failure.
3. Reporting
Unlike both DKIM and SPF, DMARC provides the sender of the email reasoning of why certain actions were performed under the policy.
DKIM (Domain Key Identified Mail)
DKIM (DomainKeys Identified Mail) is an email authentication protocol that helps to protect the integrity of emails by verifying that they are sent from authorised sources.
It works by adding a digital signature to each message, which can be used to verify the sender's identity and ensure that the message has not been modified or tampered with in transit.
A DKIM signature uses hash values which are made up of a unique string of characters, created by a Mail Transfer Agent (MTA).
Using the public key registered in the DNS, the receiver can verify the DKIM signature, by decrypting the Hash Value and recalculating the hash value from the received email.
If the two DKIM signatures match, the MTA can verify that it came from the listed domain and the email has not been altered.
SPF (Sender Policy Framework)
Similarly, like DKIM, SPF is a technical standard and email authentication technique that assists with validating and authenticating an email senders’ original source.
SPF works by creating an SPF record, that is stored in the DNS, which specifies which IP address or mail server the domain owner uses to send an email.
SPF authentication involves the receiving mail server verifying the domain by comparing the “envelop from” address in the email header and the IP address to ensure it matches the SPF record.
What does DMARC do?
Have you ever received an email that seems too good to be true? Or maybe you've noticed strange emails that claim to be from a legitimate company, but something just doesn't seem right.
Don't worry, you're not alone - many people have fallen victim to phishing scams and email spoofing.
Thankfully, there's a solution: DMARC. But what does DMARC do? DMARC stands for "Domain-based Message Authentication, Reporting & Conformance" and is a powerful tool that helps prevent these types of attacks.
Essentially, DMARC verifies that incoming email messages are coming from the domain they claim to be coming from, and if they're not, it takes action (like marking the email as spam or just outright rejecting it).
By implementing DMARC, companies and organizations can protect their customers and their brand from phishing attempts and email fraud.
So the next time you receive an email that seems too good to be true, remember that DMARC is working behind the scenes to keep you safe.
How does DMARC work?
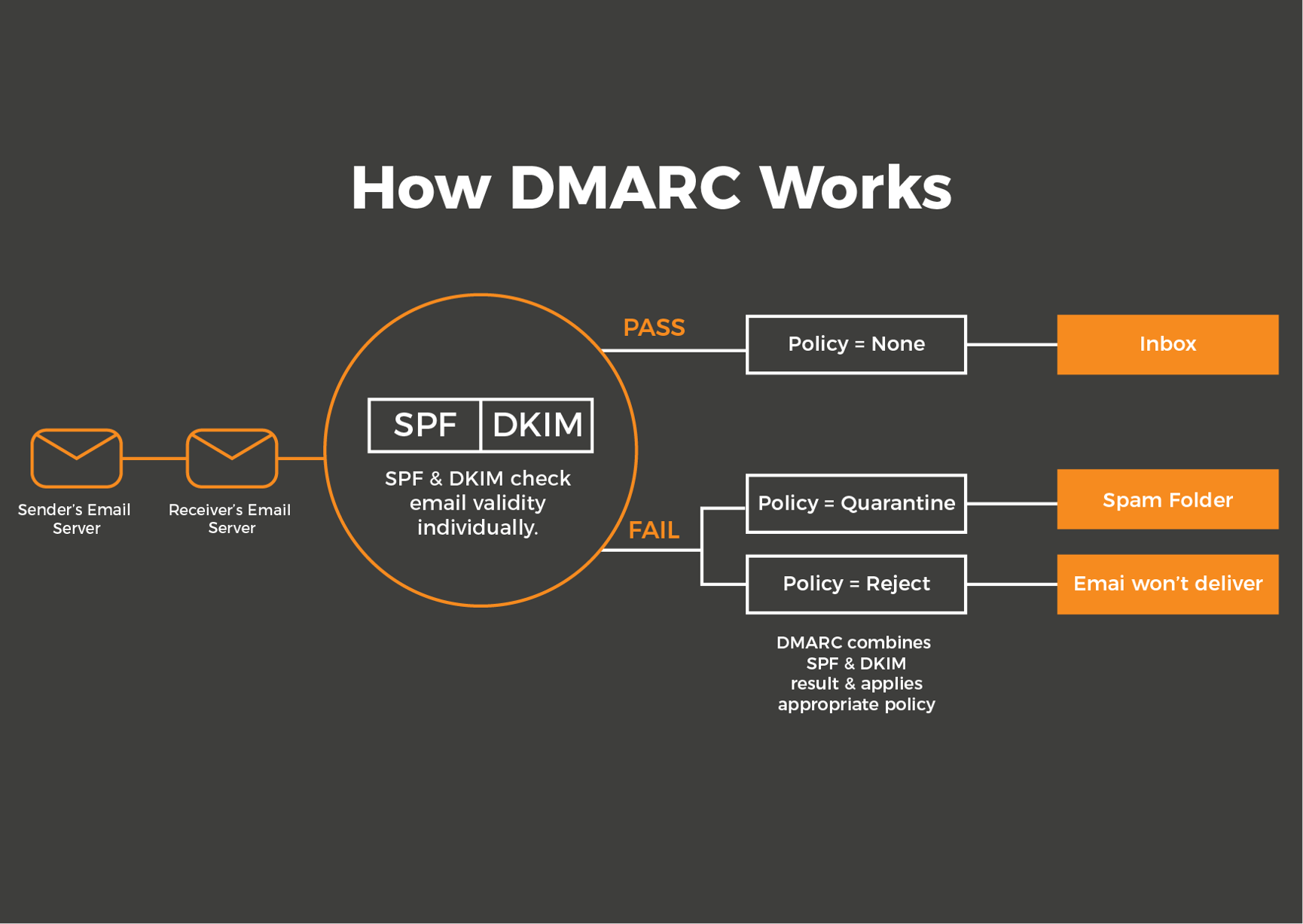
DMARC works by using the established DKIM and SPF standards for email authentication, as well as piggybacking on the Domain Name System (DNS). How DMARC works can be broken down into 4 steps:
Step 1: Domain Owner Publishes DMARC Policy
First, the owner of the domain must publish a DMARC record that outlines the email authentication policy. This is then stored on the domain DNS which can be accessed during the email authentication process.
Step 2: Mail Server Checks
Secondly, the receivers mail server will check for a DMARC policy that uses the “from” address in the sender’s email. This includes checking for a matching IP address in the senders SPF records, a valid DKIM signature, and will also text for domain alignment.
Step 3: Application of DMARC policy
Using the results of the mail server checks, the server will then either accept, quarantine, or reject the email.
Step 4: DMARC Report
The receiving server will then send a report of the outcome to the email specified in the DMARC record. DMARC reports can come in two formats: Aggregate or Forensic.
What is the difference between DKIM and DMARC?
The four key difference between DKIM and DMRC are:
| DKIM | DMARC |
| Uses encryption techniques to add a digital signature to each email message | Uses policy-based techniques to determine how messages should be authenticated and delivered |
| Verifies the authenticity of the sender | Verifies both the authenticity of the sender and whether or not the message has been altered in transit |
| Works only on outbound messages | Works on both inbound and outbound messages |
| Does not provide feedback about how emails are being handled | Does provide feedback about how emails are being handled by receivers |
1. DKIM uses encryption techniques to add a digital signature to each email message, while DMARC uses policy-based techniques to determine how messages should be authenticated and delivered.
2. DKIM verifies the authenticity of the sender, while DMARC verifies both the authenticity of the sender and whether or not the message has been altered in transit.
3. DKIM only works on outbound messages, while DMARC works on both inbound and outbound messages.
4. DKIM does not provide feedback about how emails are being handled, while DMARC does provide feedback about how emails are being handled by receivers.
What are the benefits of DMARC?
DMARC’s main benefit is that it adds a much-needed extra layer of email security to your pre-existing protocols.
As it works at the DNS level, it protects your inbox before emails even reach them. Other benefits of DMARC include, but are not limited to:
- Brings transparency to email activity
- Identify threats, spoofing and phishing attacks from a specified domain
- Reduces Spam
- Authenticates emails content and from address
- Improves email score and deliverability
- Creates reports of failed sends
- Defines policies
Does your business require DMARC?
If you’re unsure whether you should employ DMARC protocol in your business, answer one simple question…
Do you use email in your business?
If you answered yes, then the answer to if you need DMARC is also yes.
Verizon reported that 94% of malware is delivered by email, which means businesses must put more emphasis on their email security.
Using DMARC reduces the likelihood of your business’s domain being spoofed which means your customers, suppliers and all contacts are better protected.
Furthermore, being able to tell clients/suppliers etc that your business uses DMARC will make your brand look more reputable, as well as build confidence and trust amongst the business’s stakeholders.
DMARC Related Frequently Asked Questions
Should DMARC be enabled?
The simple answer is, yes! DMARC should be enable. By enabling DMARC, you are taking a proactive approach to securing your email domain, protecting your brand reputation and improving your email deliverability.
Is DMARC better than SPF?
Yes, DMARC is better than SPF. DMARC provides additional benefits. DMARC not only verifies the sending domain, but it also allows for reporting and policy enforcement.
This means that domains using DMARC can gain visibility into potential email abuse and take action to prevent it.
While both protocols have their strengths, DMARC is becoming increasingly popular due to its ability to provide more comprehensive email protection.

-2.png?width=359&height=449&name=text-image%20module%20desktop%20(4)-2.png)

.jpg?width=276&height=195&name=1-Jul-02-2024-10-07-08-8540-AM%20(1).jpg)
.jpg?width=276&height=196&name=Case%20study%20(21).jpg)
.jpg?width=277&height=196&name=10-2%20(1).jpg)

-2%20(1).png?width=298&height=420&name=text%20image%20tablet%20(31)-2%20(1).png)



.png)


