Enterprise Mobility Suite
Security for your network. Peace of mind for your organisation.
AZTech Managed Enterprise Mobility + Security
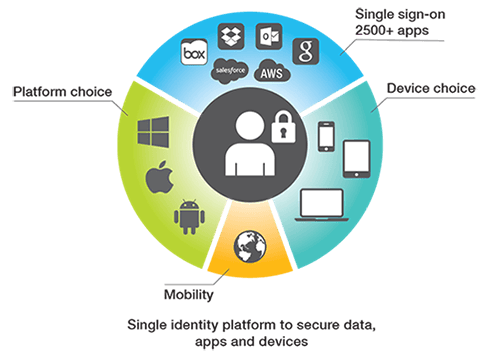
Microsoft Enterprise Mobility Suite provides identity driven security solutions that address the challenges in keeping data secure in a mobile and cloud working environment.
EMS combines Azure Active Directory Premium, Intune and Azure Rights Management. AZTech IT are an accredited Tier 1 Microsoft Cloud Service Provider (CSP). We employ highly experienced professionals and technology specialists including Microsoft Certified Systems Engineers (MCSEs) in our Professional Services Team. Overcome challenges of security and mobile working by contacting us today to see how we can assist you.
EMS + Security
Productivity without compromise
- Control identity and access to your cloud apps
- Manage mobile devices and applications
- Identity driven security
- Email Security
- Manage rights
- Manage BYOD
Azure Active Directory Premium
Azure Active Directory is a comprehensive, highly available identity and access management cloud solution. It includes core directory services, advanced identity governance, and application access management.
Intune MDM - Mobile Device Management
Microsoft Intune manages and protects data and application on any device including mobiles, tablets and laptops. Deploy, manage and even wipe corporate date from any managed device.
Azure Rights Management (RMS)
Azure rights management helps secure your data such as files and emails by using authorisation policies, encryption and identity even when it has left your network.
SSO Single Sign On
Centrally managed passwords for all you applications across all your devices. Self service portal providing secure single sign on to all your applications.
Advanced Threat Anayltics
ATA provides information on what is happening within your network by identifying suspicious user and device activity. Built-in intelligence helps against targeted attacks by automatically analysing, learning, and identifying normal and abnormal entity (user, devices, and resources) behaviour.
EMS With Office 365
EMS provides additional security for Office 365 and expands your capabilities to help you securely deliver all of your apps to any device and protect your data whether it's on premise or in the cloud.
Recent Posts

The Year of AI Agents: What Claude Managed Agents Means for Business
| April 9, 2026
AI agents are autonomous systems that work independently on complex tasks for hours, using tools, writing code, and browsing the web without human..
.png?width=400&name=AI%20Model%20Updates%20%20(1).png)
Claude Mythos and What It Means for Your Business
| April 9, 2026
On 7 April 2026, Anthropic announced Claude Mythos Preview, the most capable AI model ever built. It outperforms most human specialists at coding,..

The SaaSpocalypse: Is Your SaaS Stack Obsolete? (2026)
| February 11, 2026
Summary The February 2026 software stock selloff, triggered by Claude Opus 4.6 and GPT-5.3-Codex releases, wiped $285 billion from SaaS valuations...
Ready to discuss how to protect your corporate data?



